Remote access trojans (RAT's) are tools often used by hackers for controlling compromised targets. They've been around for quite a while, and have evolved slowly over time. Last week, the FBI took overt action against many operators of the BlackShades Net RAT, bringing it into the public eye.
BlackShades Net
BlackShades Net is a RAT that has been around for a few years. It has been the source of a few arrests, including the co-author in 2012. It was developed as for sale malware, sometimes poorly masquerading as legitimate remote administration software. It can be found being sold or leaked on black hat forums along with a user manual and setup manual.
Server
In RAT's as well as other malware, the component installed on the infected host can be referred to as the server. It controls operations on the host, in this case including actions like launching DDoS attacks and gathering information such as keystrokes and images from the web cam. From a defense perspective, this is the most interesting component.
Functionality
The features BlackShades has aren't very unique, but there are quite a few of them. Here are the features the attacker has access to:
- Control many computers at once - View Screens - Upload file - Download file - Keylogging - Ransoming files - Facebook Hijacking - USB Infection - Instant Messaging Spreading - Torrent Seeder - Bot market place (buy and sell infected machines) - DDoS - Web cam access - Manage Proxies - Block/Redirect URLs - Proxy through infected - Inject itself into other processes - Multiple persistence methods - Chat with the infected - Delay before execution - Password Recovery - Ad Clicking - Audio capture - Form grabber
Since I had a version of the client available, I decided to try out some of these features first hand to show what an attacker would see.
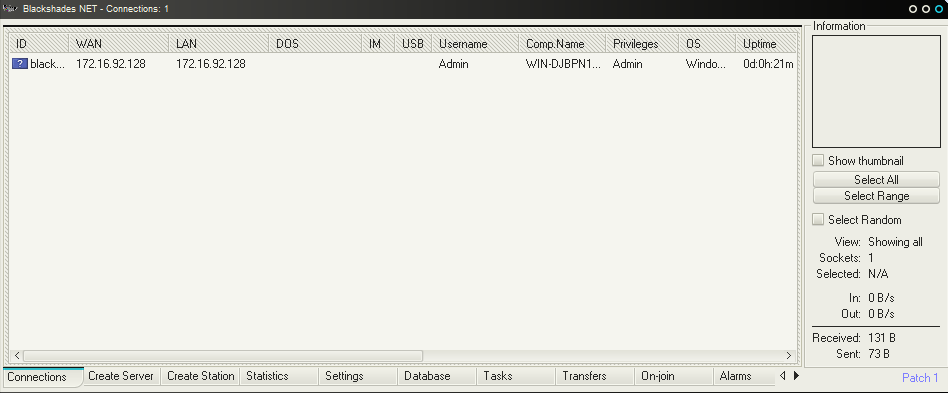
When a server first connects back to the client, it gets added to the server list.
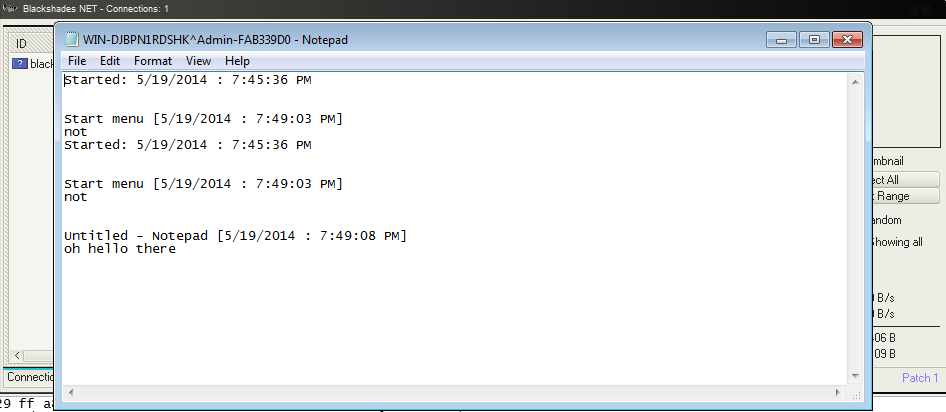
If we start typing on the compromised box, we can start to see it in the client.
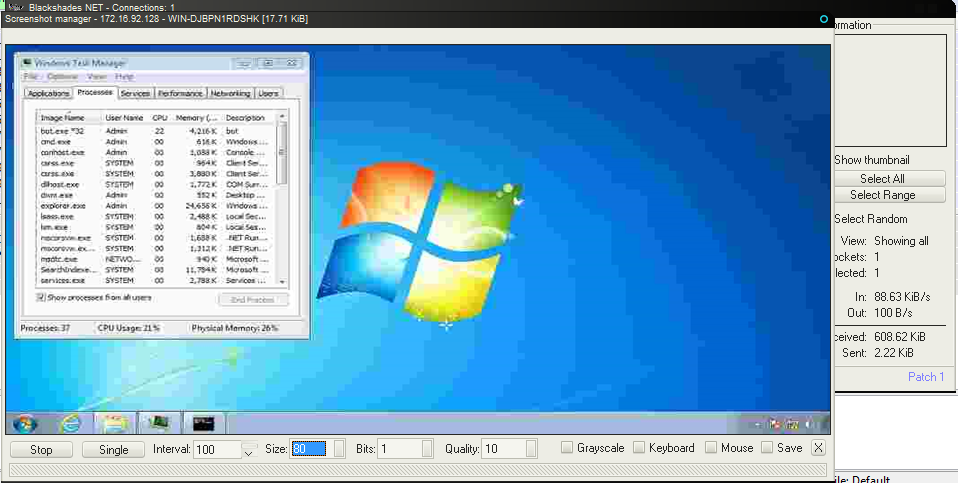
The screen shot feature acts more like an active screen viewer, automatically updating while the window is open.
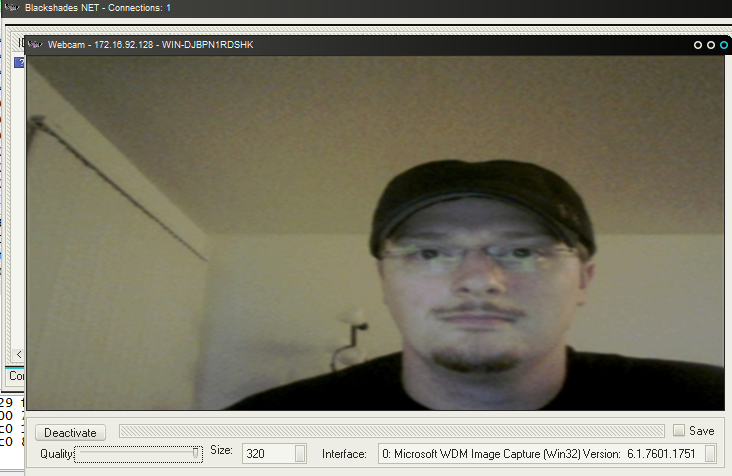
The web camera feature is intrusive, but it could be worse. When using this feature, the light on my web camera did activate. If you have a strong concern about someone accessing your web camera, I suggest a web camera cover, or opaque tape.
Static Analysis
The server is written in Visual Basic 6, which has long been as a technique by attackers. This allows them to write simpler code to do more complex operations, cutting down on the amount of technical skill required to write or add to their RAT. It also requires some different reverse engineering techniques (or tools) that are generally only used for reversing Visual Basic but can get closer to the original code.
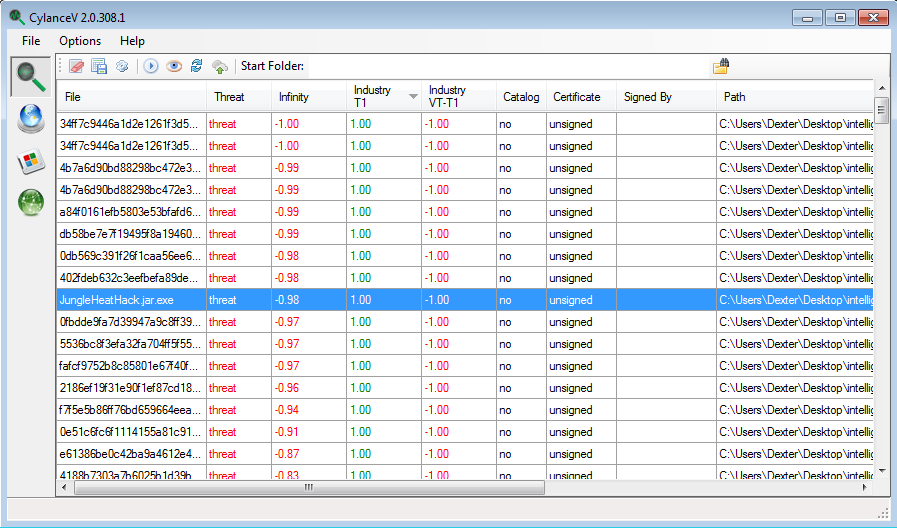
Detection
There are a large number of BlackShades samples around, and depending on how they are packed/crypted, their detection rates vary. Our machine learning-based detection method has no issue with these binaries.
Configuration Extraction
Any configurable malware needs to store some sort of configuration, and this configuration is the key to monitoring the actions of those controlling the malware. Malware developers/users are well aware of this, so they attempt to hide the configuration as much as possible. When building the server binary from the client, there is an option to build with a password, which obfuscates the configuration.
The configuration is stored in an ASCII string, which is hex encoded. The length can be variable since it stores information like the domain being used for the client. Here is a sample:
743A324C48683D60554F60784362505D3578585A3F5B636F60434F504E557636A7C95F6C9C0CAADC57057BFAE1356CB09DF213314D3E98F95DAFC37477A881AF767EC6AABC9CC463BE4F805D8FF98A34DAF3EDA24C972F5F6D9E5FD2929636890049BB1F361E43F3733FC395ADF17E18533013C22529995DA15EB58800F086554EB449347F091D0A4A91A933CA8BDB673475DD294687AD0877B283D170511E416B207F73540F20BCA5AF8957F7FB2B55C258911A0BBD2F723DBFB9D332D9868E07289C635E800728434EE45EB69596BC5D3C3137BF3244 After we decode this, we still have an obfuscated blob of information. The first 32 bytes are used as a key to decrypt the remaining bytes.
The decryption process in two steps, and the first step is seed generation. The seed value is a 4 byte integer, which is generated through a fairly complex set of bit shifts and XOR's. It generates 256-integer entries that are XOR'd against the key value. This is done incrementally, and then returned as the seed. The good news is we don't have to implement any of this if we want to statically extract the configuration.
For the decryption of the configuration, the PRNG for Visual Basic is used. The value generated from the key is set as the seed for next values to come out of the PRNG. This PRNG is powered by the following pseudo-code.
seed1 = ( seed0 * 1140671485 + 12820163 ) % (2^24)
This is actually an extremely simple and weak PRNG. Despite the size of seed values, it is cut down to 24 bits of possible values. This means that if we wanted to brute force this integer value, there would only be 16,777,215 entries we needed to try. The decryption is done by computing the XOR of the PRNG output and each character in the obfuscated blob (one iteration of the PRNG for each character).
Once the decryption finishes, we have the configuration string. The configuration string splits values with three 0x0c bytes. The order of the configuration appear in the following order:
- Controller host name - Client Control Port (TCP) - Client Transfer Port (TCP) - Bot name - File name - "app" or "tmp", determining where to install - Registry Persistence name - Active Setup Persistence name - Install - Unknown - Unknown - Delay length - Infect USB drives - Mutex name - Log file - Folder name - Unknown - "Protect Process" Here is a sample configuration string decrypted:
0c 0c 0c 31 39 32 2e 31 36 38 2e 31 2e 31 0c 0c |...192.168.1.1..| 0c 34 34 34 33 0c 0c 0c 34 34 33 34 0c 0c 0c 4c |.4443...4434...L| 6f 63 61 6c 0c 0c 0c 6c 6f 63 61 6c 2e 65 78 65 |ocal...local.exe| 0c 0c 0c 61 70 70 0c 0c 0c 77 69 6e 64 6f 77 73 |...app...windows| 0c 0c 0c 0c 0c 0c 30 0c 0c 0c 30 0c 0c 0c 30 0c |......0...0...0.| 0c 0c 30 0c 0c 0c 30 0c 0c 0c 50 44 56 45 46 4a |..0...0...PDVEFJ| 51 55 30 52 0c 0c 0c 4e 61 77 0c 0c 0c 0c 0c 0c |QU0R...Naw......| 31 0c 0c 0c 30 |1...0| Here is the same configuration string after it has been parsed:
'192.168.1.1' '4443' '4434' 'Local' 'local.exe' 'app' 'windows' '' '0' '0' '0' '0' '0' 'PDVEFJQU0R' 'Naw' '' '1' '0' Here is a quick Python (v2.7) script to extract the configuration from non-encrypted non-compressed BlackShades binaries.
import re from os.path import abspath, isfile, isdir, join from os import listdir prng_seed = 0 def is_valid_config(config): if config[:3] != "\x0c\x0c\x0c": return False if config.count("\x0C\x0C\x0C") < 15: return False return True def get_next_rng_value(): global prng_seed prng_seed = ((prng_seed * 1140671485 + 12820163) & 0xffffff) return prng_seed / 65536 def decrypt_configuration(hex): global prng_seed ascii = hex.decode('hex') tail = ascii[0x20:] pre_check = [] for x in xrange(3): pre_check.append(ord(tail[x]) ^ 0x0c) for x in xrange(0xffffff): prng_seed = x if get_next_rng_value() != pre_check[0] or \ get_next_rng_value() != pre_check[1] or \ get_next_rng_value() != pre_check[2]: continue prng_seed = x config = "".join((chr(ord(c) ^ int(get_next_rng_value())) for c in tail)) if is_valid_config(config): return config.split("\x0c\x0c\x0c") return None def extract_configuration(file_path): with open(file_path, 'rb') as f: strings = re.findall("[0-9a-fA-F]{154,}", f.read()) for s in strings: if (len(s) % 2) == 1: s = s[:-1] ret = decrypt_configuration(s) if ret is not None and len(ret) > 15: return ret return None def enumerate_paths(path_list, recursive_scan): ret_paths = [] while len(path_list) != 0: file_path = abspath(path_list[0]) del path_list[0] if isfile(file_path): ret_paths.append(file_path) elif isdir(file_path): for p in listdir(file_path): p = join(file_path, p) if isfile(p) or (isdir(p) and recursive_scan): path_list.append(p) return ret_paths if __name__ == '__main__': from argparse import ArgumentParser parser = ArgumentParser( prog=__file__, description="Attempts to extract configuration from BlackShades samples", version="%(prog)s v1.0.0 by Brian Wallace (@botnet_hunter)", epilog="%(prog)s v1.0.0 by Brian Wallace (@botnet_hunter)" ) parser.add_argument('path', metavar='path', type=str, nargs='+', default=None, help="Paths to files or directories to scan") parser.add_argument('-r', '--recursive', default=False, required=False, action='store_true', help="Scan paths recursively") args = parser.parse_args() for path in enumerate_paths(args.path, args.recursive): answer = extract_configuration(path) if answer is not None: print "{0} - {1}".format(path, repr(answer)) Identification
BlackShade servers have plenty of different reliable ways to be detected. The difficulty in identification would be in the cases where the sample was packed or crypted. Here is a quick Yara rule for identification.
rule BlackShadesServer{ strings: $str1 = "bss_server" $str2 = "txtChat" $str3 = "UDPFlood" condition: all of them } Summary
BlackShades is a remote access trojan which can be used by attackers to remotely control an infected host. It has a wide variety of features, although no particular feature is unique from others we've seen before. It is developed in Visual Basic, and stores its configuration in a string resource, which is obfuscated with a built in key. The key can be ignored in analysis though, as the configuration encryption can easily be brute forced. As always, our machine learning based detection models have no trouble detecting this malware.
- Brian Wallace AKA @botnet_hunter
Samples
00ae98940703615ed0860f3eb67d07f6 00f8ddf528425a997787ba2e30949623 010426d44345ffc6b588aa269469112c 02f3ca4afa81d4f2987ea6eef4a01c26 0315ae7b528829a66f0cb72fcbf10d2f 05fd12a1fd40f5c7466f424be8cf4e20 063e89b790c2f6c1c5f8cc6d04279385 06aff3e08ee27300157f7b652ec7e429 088230652018a2b469acbcea4407cb61 098b91cd6051de5324cb1fce05910403 0ad952ea9f6566aa7adbebc0dac9e7d5 0b80017f021d04a94dae136ea99947d0 0f2d4e12d56088a781df16408cf7528b 10bad80d8d42ffe7ed5c69ba75c40544 13129673d1ad43a3b959836526c2af3c 1390100f9778f120e1649fbf15c8b410 148c7b0d64a38631de66a08bae14faf9 17a5234ba1178df445cd9c7a8e01c9f0 183acbb6a0f166edc6bbd0a89e11af30 187033b0bc1c1ca36bd509bdb82e5553 18e8373c89f8656cdac8771df18f98d0 1cc01685b22dad0ff61a3426e66116d8 1d6e638211df7341acbaafe08517f419 1da57e9a360e008885c11393a55b88c4 2297aea1b524fbd1202a82c6c175b4c4 23b7b97ab12817c7aeb3d60a8239d311 253ba0a2875fbde86328e53e50e1e94a 2542681e4994c7574e4b2d24356840a5 270edbdc84b8dbf5a4a758887e57701e 272937500bac50d098773c8702017e29 2be30933aae9569fafcc98a8449e6e10 2e5ee3108f27b0ff1f13c248ca3e633b 32a5eaa52ed95b68b44571912b339b01 332ec62c3b46c3c1e07c216a00eaa667 34c4bf0d45b06fecaabb68d4b3b6af00 35fa0bd99794b376f8476b1c6296b8e0 370880b81f6fd28743511ee7f6fd932a 38dc2926edfed320ba36d7293cabbe06 3eb8232d0aacc59a302a4cf3d0799a1f 4260779961f0be35372249d232d72c6e 428bd8cb235d69f95e555a9a3ecd7ab1 4cbe936016aba6c84cd24568503a6f3b 723b0f90ff6bd405e4edf774f3f23716 73da95f222d43279186b0a9957f05aef 75a406c6c9ed917fc64de7a1410a6649 7ab66b469f8ca25af17dcbc284682aab 7c0fc6ac6f87afe2c33485d554d4ec99 80a28ff03e6f9ef5c24b0131970555a1 9518d2e5edbbe8e6b42cc0ee9c9f611a 97226907a3d10449469e99f7e387f0fe 974ba07b360754c81be698b0f456054c 97b456dd8b6f9b42ced4bf199741d60e 993c9c6a48614f0567a6745460fc1690 99b2f473e2a51b53a9ad8cb16f78d6a2 9b3d22413240bf011796e6ae8c9592d0 9bcfe44a9e0a822555faf56ac1f2670c 9bd8c077493a5bd38f676e755f343d27 9c85525cb1b06ad13487c7d07b8cb37b 9e928e69013d1fbe59b37549fae7c277 9f09d98ef23d5559db3fa08fe5f61935 a04f95ee8cd8f3928df2fcba4be08794 a0556d4f9f11558589677fb9dc18682b a0a730833efcf3e5197bacfed365b9d5 a119e82c4be8c17057974cfb14ef8f44 a11c20d37b06f4db690455f8ed1f5232 a1e0327e96fe38076e885d4d413be495 a20e2f7d04b92d43894244fea5cebce5 a265e4201350c3ac2b6e1ea8485997c9 a27c3505131ff11b1ca60d3771c3488d a335b164632ce6d2e8f5cb4f210d45f5 a3581ad71455b86298ab8a7ab6bd2f79 a7468fa3ad8627778dc533e485f7231b b4c76f0aacb77170e152083a5cb4bcba c5b60451a7cdbc0943fc81c7815a4e06 c762693243797e2e62c6e0a89811b3af d1f67c7601151ae90964ffbe14192d7e da48261b4e2ee16a77a32a5a66d13da1 dc292fa1522e416afdec7077d1a078da e97f600ed1dc74ab5f47345908157d4b f524a40447409db7c1f9b56bf4b0858c f6197d6bda0c0be0d289b5b8336980ff