ANTLabs InnGate devices are a popular Internet gateway for visitor-based networks. They’re commonly installed in hotels, convention centers and other places that provide temporary guests access to a WiFi connection. If you’ve ever used WiFi in a hotel, you’re familiar with these types of devices as they are typically tied to a specific room number for billing purposes.
The Vulnerability
CVE-2015-0932 gives an attacker full read and write access to the file system of an ANTLabs’ InnGate device. Remote access is obtained through an unauthenticated rsync daemon running on TCP 873. Once the attacker has connected to the rsync daemon, they are then able to read and write to the file system of the Linux based operating system without restriction.
When an attacker gains full read and write access to a Linux file system, it’s trivial to then turn that into remote code execution. The attacker could upload a backdoored version of nearly any executable on the system and then gain execution control, or simply add an additional user with root level access and a password known to the attacker. Once full file system access is obtained, the endpoint is at the mercy of the attacker.
How it Works
A vulnerability that allows for full file system access that can easily lead to a complete compromise of the system must need an advanced exploit, right? This couldn’t be further from the truth. In fact, any *nix system which has the rsync command available is capable of exploiting this vulnerability in a few keystrokes.
An attacker would confirm the presence of an ANTLabs InnGate device by running the following command (IP has been censored).
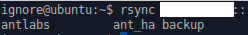
This lists the available rsync shares. The attacker could list the files in the root of that share by running the following command:
Anyone familiar with Unix/Linux based operating systems will recognize this as the root of a file system.
Rsync also has a number of commands for uploading and downloading files, which are covered in great detail in the rsync documentation. With the rsync daemon allowing for anonymous read and write access, the attacker has many options.
What Could an Attacker Do?
One of the first things that came to mind while researching CVE-2015-0932 was last year’s APT campaign dubbed DarkHotel. Discovered by Kaspersky Labs, the campaigns focus was to infect Internet gateways at Asian luxury hotels in order to compromise high-profile guests. While the DarkHotel campaign was clearly carried out by an advanced threat actor with a large number of resources, CVE-2015-0932 is a very simple vulnerability with devastating impact. The severity of this issue is escalated by how little sophistication is required for an attacker to exploit it.
An attacker exploiting the vulnerability in CVE-2015-0932 would have the access to launch DarkHotel-esque attacks against guests on the affected hotel's WiFi. Targets could be infected with malware using any method from modifying files being downloaded by the victim or by directly launching attacks against the now accessible systems. Given the level of access that this vulnerability offers to attackers, there is seemingly no limit to what they could do.
Let's assume an attacker has compromised an InnGate device at a hotel with this vulnerability, and has obtained shell access via SSH and an account they created for themselves with root access. The attacker could then simply run tcpdump, which is present on these devices, to dump all network traffic going through them. This would allow an unsophisticated attacker to gather any plaintext communication sent through the gateway of the affected hotel, convention center or data center.
A slightly more sophisticated attacker could use a tool such as SSLStrip in order to attempt to downgrade the transport layer encryption in order to increase the amount of plaintext credentials gathered. This attack gives the threat actor incredible leverage over their targets including making OpenSSL vulnerabilities easier to exploit.
It Gets Worse
These attacks presume the attacker is going after guests of the hotel, but this vulnerability also gives the attacker access to a computer the operating organization owns. In some cases, we observed InnGate devices that were integrated into Property Management Systems (PMS). In cases where an InnGate device stores credentials to the PMS, an attacker could potentially gain full access to the PMS itself.
Wikipedia provides with an excellent summary of a PMS’ capabilities:
In the hospitality industry a property management system also known as a PMS is a comprehensive software application used to cover some basic objectives such as coordinating the operational functions of front office, sales and planning etc. Automate hotel functions like guest bookings, guest details, online reservations, point of sale, telephone, accounts receivable, sales and marketing, banquets, food and beverage costing, materials management, HR and payroll, maintenance management, quality management and other amenities. Hotel property management systems may interface with central reservation systems and revenue or yield management systems, front office, back office, point of sale, door-locking, housekeeping optimization, pay-TV, energy management, payment card authorization and channel management systems.
If this PMS controls multiple locations, the attackers could potentially leverage that access to infect the other branches of an organization.
Prevalence
This vulnerability allows for complete compromise of the vulnerable system, but if there are only two running in the world, it’s not really a big deal. In order to test this, we fired up the IPv4 scanning tools Brian uses to hunt for botnet panels. After scanning all public addresses on IPv4 for vulnerable devices, we identified 277 devices which could be directly exploited from the Internet.
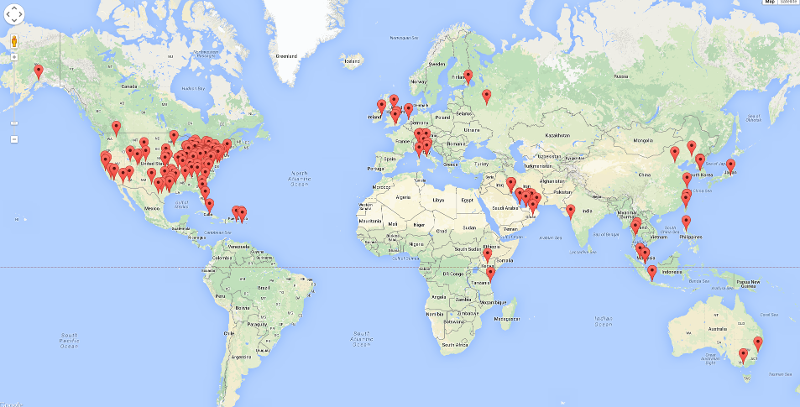
As can be seen in the map above, these affected devices are quite spread out over the world. In fact, there are vulnerable devices in 29 countries including the United States, Cuba, Australia and Italy.
The affected nodes also include quite affluent hotels. Listing those vulnerable devices at this time would be irresponsible and could result in a compromise of those networks. Take it from us that this issue affects hotels brands all up and down the spectrum of cost, from places we've never heard of to places that cost more per night than most apartments cost to rent for a month. The Cylance team is working to alert the affected organizations.
Remediation
A vendor supplied patch will be released on March 26th, 2015, addressing CVE-2015-0932. The vulnerability can also be mitigated by blocking the unauthenticated RSYNC process from internet access, a simple inbound TCP-DENY on port 873 on the upstream network device from the affected InnGate device.
Conclusion
CVE-2015-0932 is unnerving not only a due to what it affects, but also how simple it is to exploit. The Cylance SPEAR team is committed to responsible disclosure and research that helps to make the world just a bit more secure. It’s frightening to us as security researchers just how much of the world’s infrastructure isn’t properly secured but every so often we run across companies that are willing to work with the security community to fix vulnerable products. ANTLabs, the creator of the vulnerable InnGate device, should be commended for their response to our notification of the vulnerability. We reported this vulnerability to US-CERT on February 12th and a patch was scheduled for release by ANTLabs on March 26th. It’s not often that vulnerability reporting goes smoothly and ultimately results in a timely patch from the vendor.