In the world of security, you have number of tools to help you make difficult decisions - some built into your security stack and others available as free resources that can be found online. Today, I would like to discuss the latter.
I will begin by presenting you with a problem. The decision you must make is based on the images below; more specifically, you must decide which .exe file is safe to run, and which one is not.
To generate these two images I used OPSWAT Metadefender, a free-to-use vulnerability-scanning tool which utilizes the decision engines of a vast majority of the antivirus (AV) tools on the market today.
As you can see in the screenshot below (Figure 1), the first file I uploaded is flagged 21/40. This number means that 21 AV engines on OPSWAT have marked this file as malware and the other 19 have marked it as ‘Goodware’ - making it ‘possibly’ unsafe to run.
Here, we do not get a clear ‘Yes or No’ answer about the safety of this file. We must make our own decision about whether this program should be allowed to run in our environment. It’s not an optimal result, but it’s a result nonetheless and marginally better than taking a wild guess.
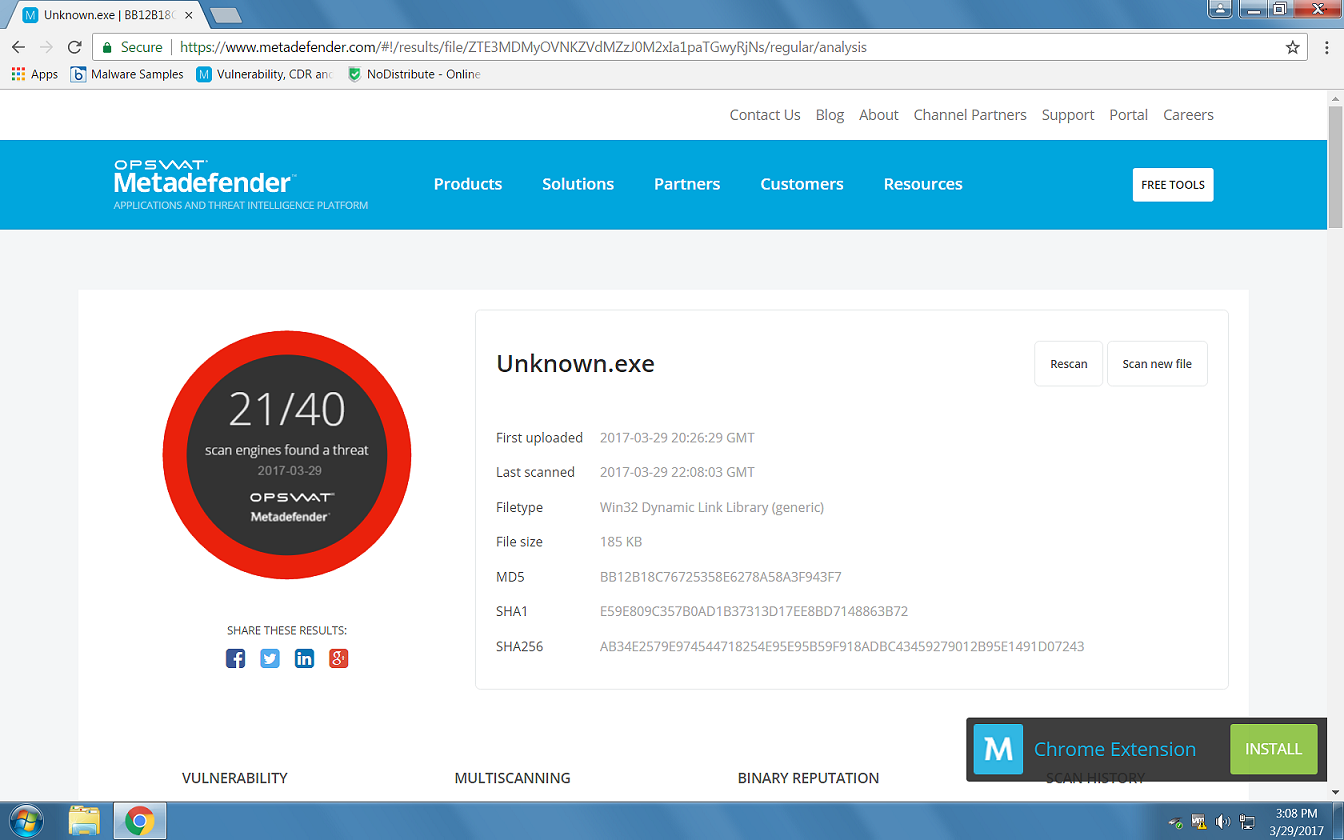
Figure 1: Unknown.exe File Rated ‘Possibly’ Unsafe by Metadefender
Given these results, I (along with most other security professionals) would decide NOT to let this run in my environment without further analysis.
Now, let’s take a look at the second example:
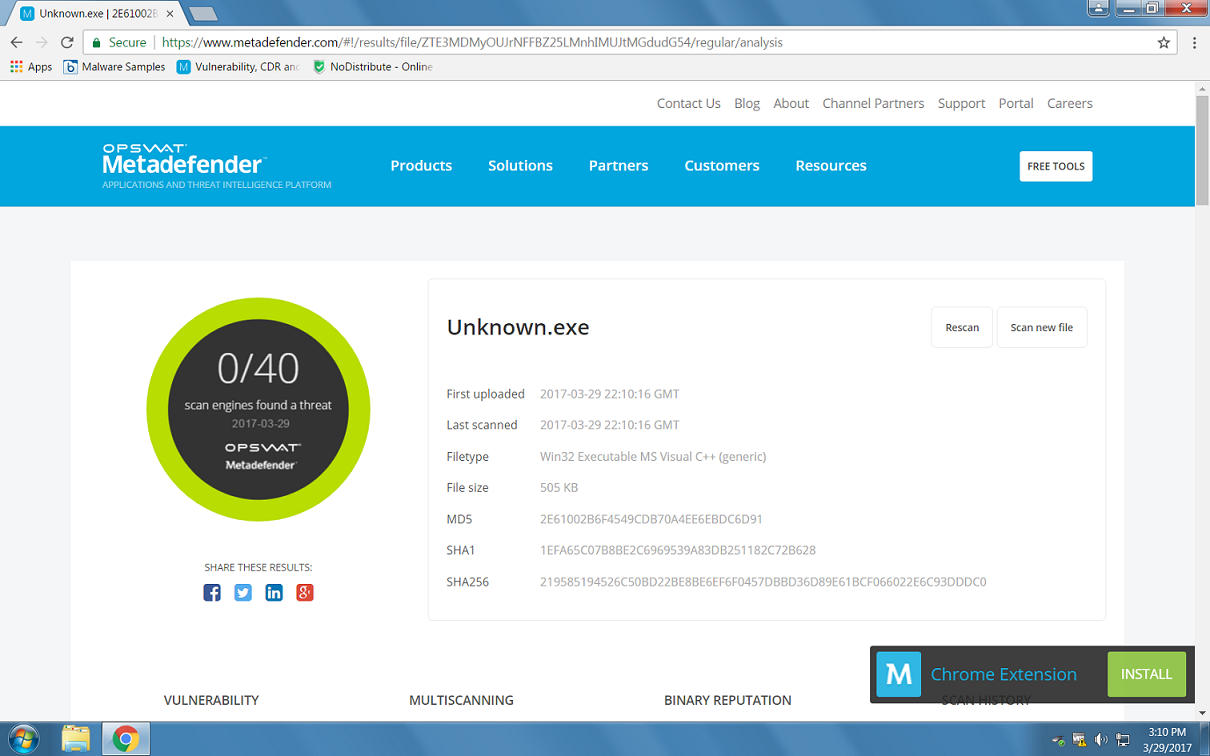
Figure 2: Unknown.exe File Rated as ‘Zero Threats Found’ by Metadefender
In this next example, we can see that all 40 available engines on OPSWAT have marked this file as “Not a Threat”. Looking at this result, you would probably feel comfortable letting this file run in your environment.
Would YOU let it run, based on this available data?
Fantastic, I Let It Run. Now What?
Now, you have just introduced malware into your environment, by allowing the .exe file from Figure 2 to run. SPOILER: The two images above show the exact same malware file, except the file’s code has been altered very slightly in Figure 2. This is something attackers do regularly, rather than expending time and energy writing malware from scratch.
I pulled this example ‘Unknown.exe’ file from a malware repository in which I was searching for malware with a high conviction rate. For the first test, I made minor alterations in the code, simulating what a malicious attacker would do, and tested it by uploading it to OPSWAT. I received a score of 21 out of 40. Not too bad, but not the convincing result that I, a would-be malicious attacker, was looking for.
Then, in the second image, I altered the malware file one more time and was able to bypass all 40 engines. I’ll say that again, because it’s important. My minor alternations to the malware .exe file succeeded in allowing the file to bypass 40 online scanning engines, by essentially turned the file into a zero-day – a never-before-seen threat.
Why Is This That Big Of a Deal?
Threat actors use the exact same resources that are available to both security professionals and regular users to increase their own chances of success. They use the conviction engines that are free to use online, to test and retest their malware in progress in their search for that sweet spot where their code is not going to be detected by free online resources.
They are basically using good resources to do evil. And they’re using the easiest and cheapest methods that require the least amount of effort, in order to successfully bypass your good judgement and get to your data.
Why Do These Services Exist If They Can Be Exploited Like This?
According to AV-Test.org, there are approximately 390,000 new malicious programs created each and every day. That’s a lot of signatures that need to be created to protect against them, so AV engines share intelligence with each other to help keep up with this ever-increasing volume of malware.
These engines not only use the available data to create their data files, but they also upload unknown files to help them make crowd-sourced decisions about whether or not to let a certain program run.
Now, the same thing can be said about the various threat indicator reports that come out daily. Once these reports make it into the world, the very same threat actors they identify also gain access to these reports. They use them to learn which of their tactics have been discovered by ‘the good guys,’ and pivot accordingly. While the intention behind these reports is honorable, they are also helping the very ‘bad guys’ they aim to warn us about to make more effective malware.
So What Can I Do?
The first thing to do is to weigh up the pros and cons of using multi-engine AV scanning services. The next step for the security-aware individual is to always keep in mind that any service that is publicly available to identify a threat can also be used by a threat actor to determine their own chances of success. Bottom line: you need a way to determine what is a threat and what is not a threat, without relying too heavily on publicly available resources that are available to the bad guys too.
That’s where the power of artificial intelligence (AI) and machine learning (ML) come to your aid. AI ‘knows’ exactly what innate properties of malware suggest that the file should not be trusted. This part is crucial, because it allows you to screen for and block unknown variants of malware (such as zero-days) from running. You need to stop malware its tracks, before it can get into your system. You don’t want to be the Patient Zero who runs the fun new zero-day and gets infected.
AI allows you to scale – rather than looking at one file at a time with hundreds of characteristics, machine learning allows you to look at MILLIONS of file characteristics in real-time, across multiple files, to determine exactly what is a threat and what is not. The decisions are all made locally using a lightweight agent that won’t hog system resources. The agent doesn’t require constant Internet connectivity to run, and only needs to update itself every 6 months or so. So, no daily/ weekly bandwidth-hogging, productivity-sapping DAT updates and no need to constantly restart your machine to apply the latest updates.
Still don’t believe me? You don’t have to. Test for yourself using files that you know aren’t safe. Try uploading them to these free online services and see what result you get. Then, test them against Cylance. Only by testing yourself will you learn the truth.