Do you know the story of the ant and the grasshopper? I won’t retell it, but basically the ant works all summer to be prepared for winter and the grasshopper plays all summer only to die slowly and painfully in winter because it didn’t prepare. Or something like that.
It’s just really a nice morality tale with no plot holes, inaccuracies, or unresolved issues. And the point of the story is that you work before you have the problem. We know that in cybersecurity, because when it’s breach o’clock you better be ready.
When it comes to breaches, the best advice I can give you is don’t let it happen. But to get there you need to be like the ant and put in the effort. But what effort?
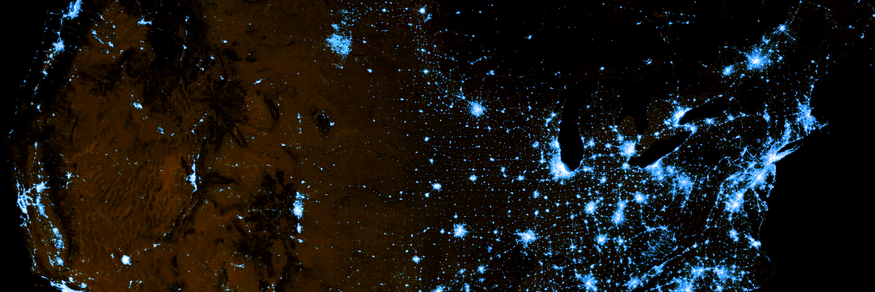
There is one problem. The problem is that a small network in an average 20-person office still has an enormous attack surface. Galaxy-sized enormous. To be more specific, for that small network there are more ways that a kill chain can play out than there are hydrogen atoms in the known universe.
That’s a lot to defend, so you need tools to help you create and maintain your breach defenses or you’ll never get it done. That’s not an exaggeration either, it’s just basic math. And not just any tools, but scalable automation tools that do what automation does best, verification tasks done quickly, consistently, and relentlessly.
Before I go on, let me just tell you it gets worse. Yes, I know I said “there is one problem” above, but really I have two problems for you, because I want to upset twice as many people. The other problem is that even if you’re willing to put in the effort to be secure, you probably don’t have enough people to do it. So really the only things that can stop you are basic math and a total lack of a trained workforce. So, still a problem even if you invested in a snappy calculator before you got to this paragraph.
The need for cybersecurity analysts will reach 2.2 million by 2020 in many accounts, most of which are not mine, so therefore plausible. Which means short of cloning your bad self to make many hands and thusly light work as per laws of hand-physics, you’re going to need fake people. By that I don’t mean those Facebook friends who tell you they miss you, I mean Artificial Intelligence (AI). So, whereas better judgment is the answer to how not to friend fake people, AI is the answer to a sparse workforce.
The cybersecurity industry has responded to this problem by improving existing practices by adding specific breach-prevention tactics. It’s a total ant move of preparation before the frigid, breach winter comes.
Shrinking the Pool of Attackers
The increase in the development of threat detection services has been an interesting twist for improving risk management. Generally, risk is reduced by shrinking your attack surface. But being able to protect yourself from emerging threats lets you shrink the pool of potential breaches, which also reduces your risk.
Shrinking the pool of attackers capable of breaching your infrastructure comes in many other flavors, like reducing attacking bots with better CAPTCHA-like services, reducing potentially successful human attackers with randomly dynamic services, and reducing opportunistic attackers by assuring existing security solutions are configured correctly and able to handle contemporary attacks.
The company Cyel cleverly shrinks the pool of attackers by making data slippery. They use deception, decoys, mutation, and literally moving the data around to make it hard to get to.
Verifying Trusts
All the major breaches in the last five years were caused by a third party. Yes, you heard that right. The criminals exploited a “trust” to get in through employee phishing, vendor access, and partner privileges.
Your vulnerability scanners don’t verify if the latest branded attack makes it past your IDS. Your penetration testers don’t tell you daily which of the thousands of malware types slip through your antivirus and onto employee desktops. And your IDS and your antivirus will only tell you what it blocked.
So not only are you unaware of how exposed you are right now, but you’re completely unable to hold your security vendors accountable for the threats they aren’t covering. And the last five years of breaches prove you don’t want to have to blindly trust your security vendors.
The way this gets done is like how Picus Security did. They make a breach scanner that’s like a vulnerability scanner that continuously tests all security systems in production, even those third-party monitored, by passing real attacks through them to make sure they can catch them.
Separations
The constant increase in new technologies and gadgets have led to Bring Your Own device (BYOD) denials in many companies which affects productivity and efficiency. And seeing how much people love their iPhones, maybe even happiness. The security industry responded with next generation firewall technology to better manage compartmentalized networks that let employees run their devices in micro-segments of one.
Segmentation is probably one of the easiest and most powerful ways to protect against BYOD abuse, as well as the spreading of malware they can bring in. The security product that took separation to heart is Qubes OS. This open-source operating system uses the Xen hypervisor to provide secure compartmentalization called qubes.
Improving Your Security Workforce
Putting security in the cloud has been the answer to lightening the load on your existing security workforce. It also increases your flexibility since the security maintenance staff can work remotely now to maintain security configurations in the cloud. This lets you move your infrastructure around to scale or relocate as you need. It also increasing your chances of finding an expert security analyst rather than having to be satisfied with just those willing to live in your neighborhood.
But not everything works in the cloud, therefore there’s been a stronger push for artificial intelligence to punch the clock for you due to the security analyst shortage. AI can already excel at many of a company’s security tasks, often with the analysis ability of a trained analyst and the tenacity of an angry raccoon.
One of the companies that’s really integrated AI successfully is Cylance. The CylancePROTECT® product uses AI to remove the need for an expert attack and malware analyst sitting at your SIEM 24 hours a day. This makes the product really good at predicting behaviors that lead to breach-level attacks and blocking them pre-execution.
Recovery
While we like to think it won’t happen to us, we know that there’s a chance it will. One day we can all win the breach jackpot of negative dollars in our bank accounts. That’s what keeps us up at night and keeps the security industry busy at figuring out ways to get back to business as quickly as possible.
There’s been a good mix of work on improving back-up and recovery solutions here, getting back to the baseline, network tracing forensics some with honeynets with honeytokens, and even a whole genre of “if I can’t have it neither can you” remote-kill and remote-delete solutions.
No tool has gone farther in breach recovery than Canary. With its deceptive technologies of honey pots and honey tokens, the canary will alert you when someone’s messing where they shouldn’t be messing and even track it to where it’s being offloaded.
As your business grows, so do the problems you’re exposed to. You need to constantly modernize your cybersecurity posture and specifically include breach prevention. You can’t just run your business off a bunch of security devices and expect to be safe. You need to prepare for breaches before they come and not scramble for solutions afterward.
Be like the ant, not the grasshopper.