“All warfare is based on deception”
-Sun Tzu
Background
May 2018: a Latin American bank watches a nightmare unfold in real-time. Employee computer systems drop like dominoes, transitioning from productive workstations to useless black screens. First dozens, then hundreds, then thousands of PCs succumb to the virus.
The culprit, MBRKiller, spreads like wildfire through the institution’s infrastructure claiming every vulnerable system in its path.
Contrary to appearances, the goal is not to destroy the bank’s operational capability. The mayhem wrought by MBRKiller serves as a distraction to obfuscate the real intent of the attackers – stealing funds from the SWIFT money transfer system. By the time the ruse is discovered, the cybercriminals have walked away with $10 million.
MBRKiller Analyzed
MBRKiller, as the name implies, destroys the master boot record (MBR) of a system thereby rendering it inoperable. It makes no contact with command and control (C2) servers and performs no guided networking. It simply destroys.
Cylance threat research analysts dissected MBRKiller using IDAPro and various memory analysis tools. Here is what they found.
This malware is executed by the System.dll in “%Temp%/ns{5 random characters}.tmp”
(Figure 1):
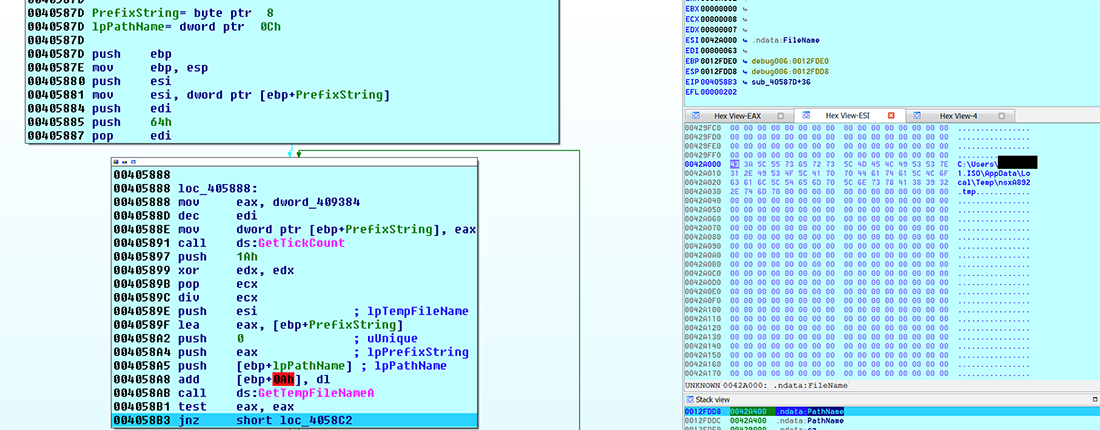
Figure 1: System.dll executes the virus
MBRKiller is packaged by VMProtect, though tools like PEID have difficulty making this determination without assistance (Figure 2). IDAPro was used to confirm the packer:
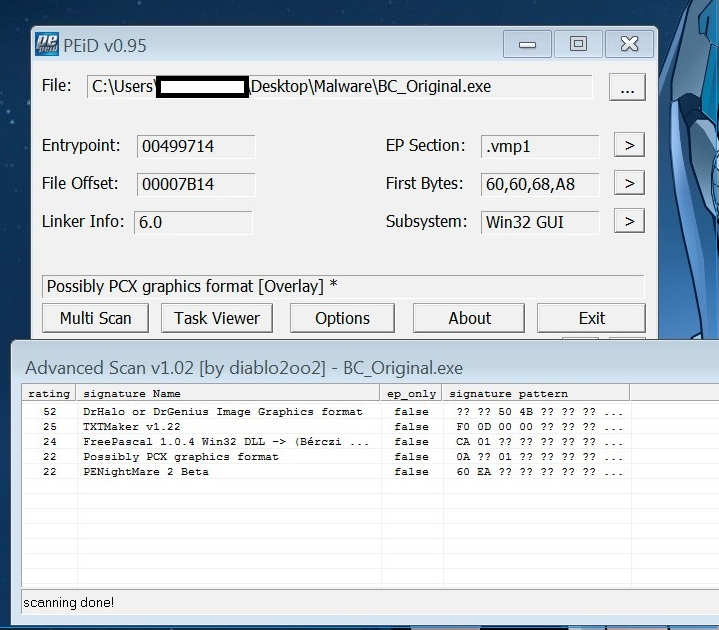
Figure 2: PEiD misidentifies the binary as a PCX file
Identifying the correct packer is vital to determining the additional capabilities of a threat. In this case, VMProtect comes loaded with an array of anti-analysis and anti-debugging operations (Figure 3):
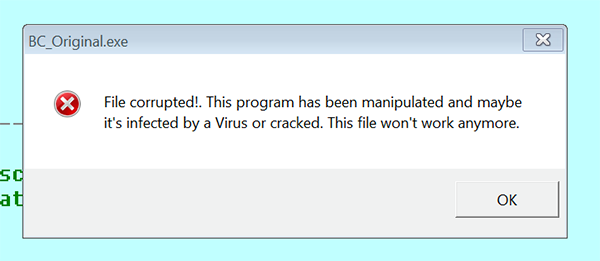
Figure 3: VMProtect resists giving up information on the malware executable
An examination of leaked source code reveals that MBRKiller possesses considerable functionality, including:
- “BHO”: a module designed to intercept and replace pages in the Internet Explorer browser
- “kill_os”: a module designed to erase the MBR
- “Loaders”: build NSIS scripts designed to install malware
- “Mimimod”: a modified version of the “Mimikatz” program, used to obtain user credentials
- “ID”: an algorithm for obtaining the unique number of the infected machine
- “BSShide”: a module designed to hide payment orders in the Business Support Systems (BSS). SWIFT money transfers are part of the BSS.
- “Antidetekt”: a module designed to detect virtual environments and sandboxes
- “UAC”: a module to bypass the User Account Control (UAC) protection
- “RDP”: modifies the OS for the potential simultaneous operation of several remote users in the system
- “VNC”: provides remote PC control with backconnect capabilities
- “DLL Side-Loading”: used to install a keylogger and to provide communication with the control panel. Enables installation and operation of other modules.
- “Control panel”: used to maintain visibility into infections and install additional modules to the infected host
- “Builder”: a program designed to collect Trojan modules in one executable file
- “MWI”: a collection of exploits, part of the “Microsoft Word Intruder” tool widely available to cybercriminals
Killing the MBR
Once MBRKiller infiltrates a system it destroys the MBR (Figure 4). The following API calls are used to overwrite the system:
${ForEach} $7 1 ${OVERWRITE_COUNT} + 1
System::Call “kernel32::SETFILEPOINTER(i, i, *p ,i) i (r2, r4, r3, ${FILE_BEGIN}) .r8”
${If} $8 <> -1
System::Call “kernel32::WRITEFILE(i, i, i, p, i) i (r2, r5, r9, r6, ${NULL})”
System::Call “kernel32::FlushFileBuffers(i) i (r2)”
${EndIf}
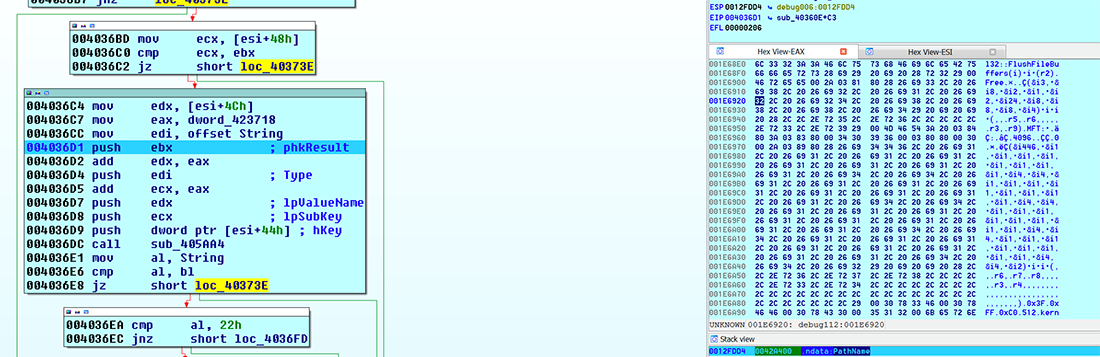
Figure 4: MBRKiller destroying a system
Why MBRKiller is Important and Why You Should be Concerned
MBRKiller is extremely destructive. It renders workstations useless resulting in both a complete loss of data and untold hours of productivity. It is a new variant of an older threat (KillDisk wiper) which indicates threat actors are actively modifying the malware for contemporary use.
It is likely that this same threat group unsuccessfully attempted an attack against a Mexican bank in January of 2018. Achieving success in Latin America may embolden this group to carry out further attacks – making MBRKiller an active threat to institutions everywhere.
Cylance Stops MBRKiller
CylancePROTECT® has been capable of identifying and stopping MBRKiller since March of 2016. This gives us a predictive advantage over the malware of roughly one year, eight months. By using highly trained artificial intelligence and machine learning models, Cylance was prepared for MBRKiller long before its creators coded its first line.
Our DNA-level understanding of malware allows Cylance to implement an effective prevention-first strategy. By understanding the behaviors, traits, and features of malware, CylancePROTECT can preemptively stop new and emerging threats like MBRKiller.

