Threat actors often take advantage of political turmoil. And this year, exploiting the invasion of Ukraine by playing on human emotions has become a primary theme. One example was documented by the Computer Emergency Response Team of Ukraine (CERT-UA), when it reported its findings on HeaderTip, a backdoor targeting Ukrainian infrastructure.
HeaderTip is believed to be tied to an APT group named Scarab, which has been linked to China. The threat group previously targeted the U.S. and Russia, but HeaderTip is Scarab’s first known attack targeting Ukraine after the Russian invasion. This backdoor is one of the first examples of attackers linked to China taking advantage of the war in Ukraine.
From a social engineering point of view, HeaderTip attacks take a similar approach to other malware such as SunSeed, utilizing the Ukraine invasion to manipulate individuals into falling for phishing attacks.
HeaderTip Backdoor Attack Chain
In this backdoor attack, a threat actor will send out a phishing email that contains a file, which claims to be from the National Police of Ukraine. A message in the file describes the need to preserve video evidence of crimes committed by the Russian military. When the EXE file is launched, HeaderTip covertly loads in the background.
This attack strategy feeds on the desire to discover and preserve information about the war, which can feel crucial to Ukrainian residents, those who have been forced to flee, and people in neighboring countries. Threat actors such as Scarab show no compunction about weaponizing this hostile situation.
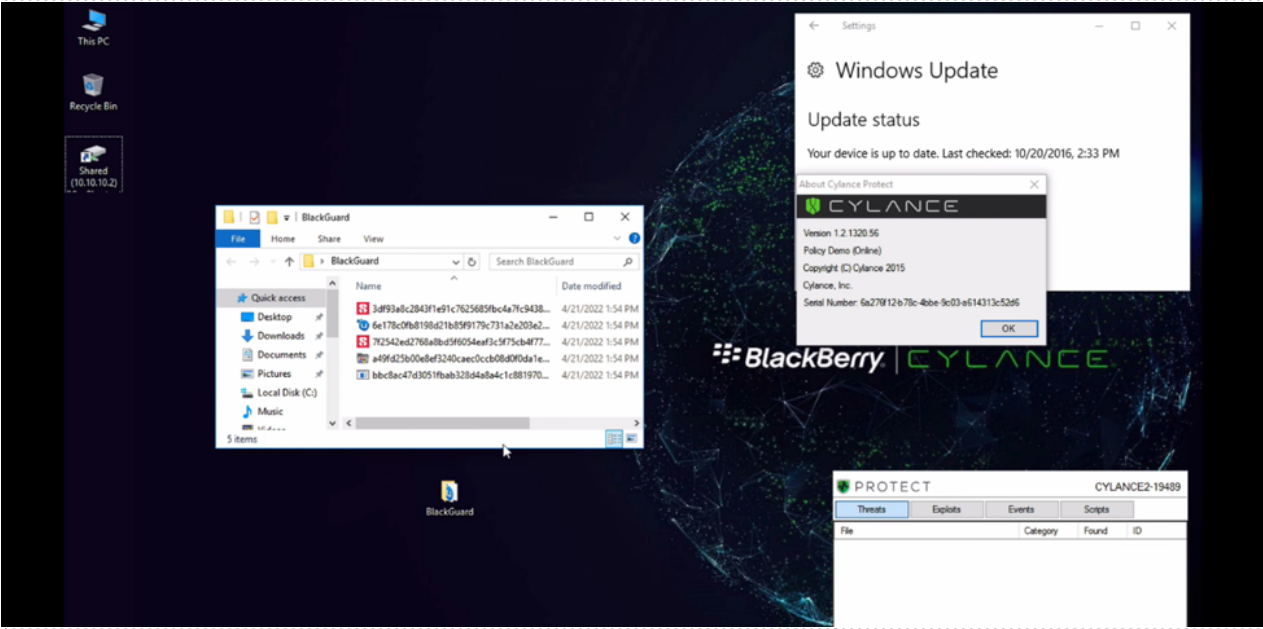
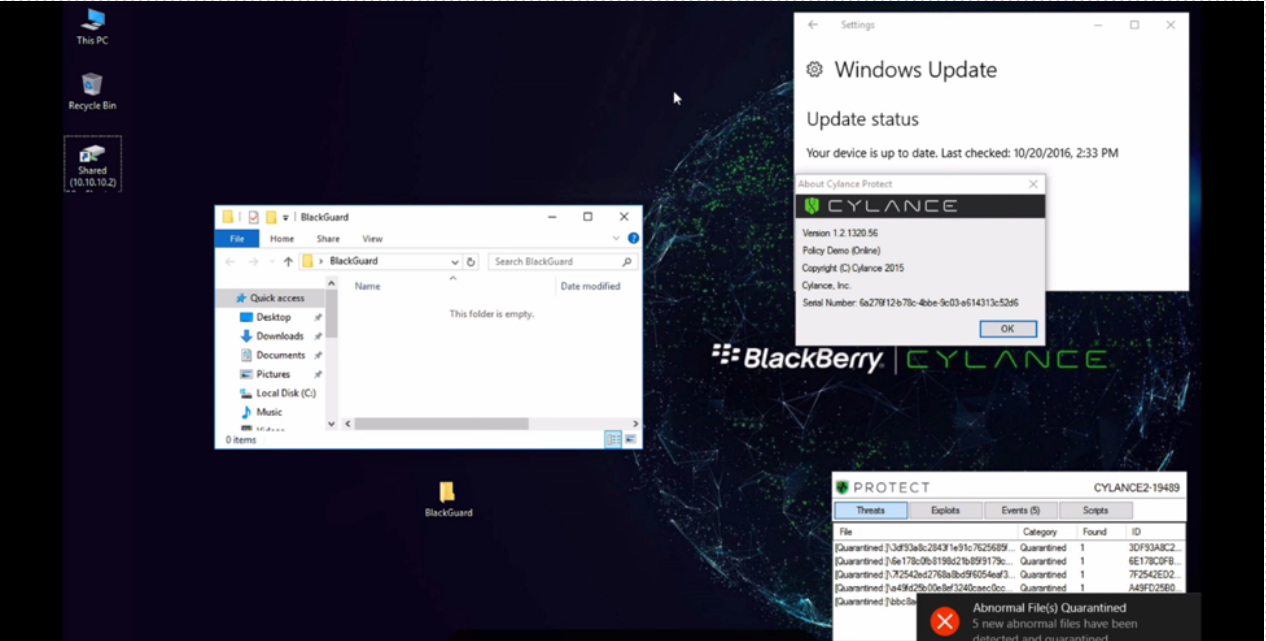
BlackBerry Prevents HeaderTip Attacks
Watch our demo video below to learn more about HeaderTip attacks, and to see how BlackBerry prevents them using our AI-powered endpoint protection solution, CylancePROTECT®.