Secure Communications Use Cases for Government
Government, military, and law enforcement agencies have something in common: Their people and their data are targeted for espionage through intercepted and spoofed communications. Off-the-shelf or consumer-grade communications options can leave your organization, your people, and your compliance status at risk. And so can many mobile security tools that come bundled with other products.
I recently spoke about secure communications use cases for government, and I’ll describe three of them in this post.
Communications Interception and Espionage
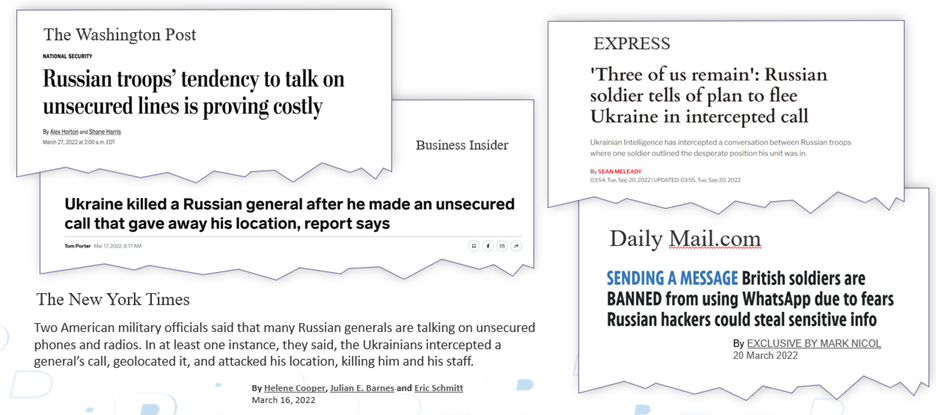
The ongoing conflict between Russia and Ukraine is just the latest example of insecure and intercepted communications. I wrote about some lessons learned early in the conflict, echoing headlines from news publications around the world.
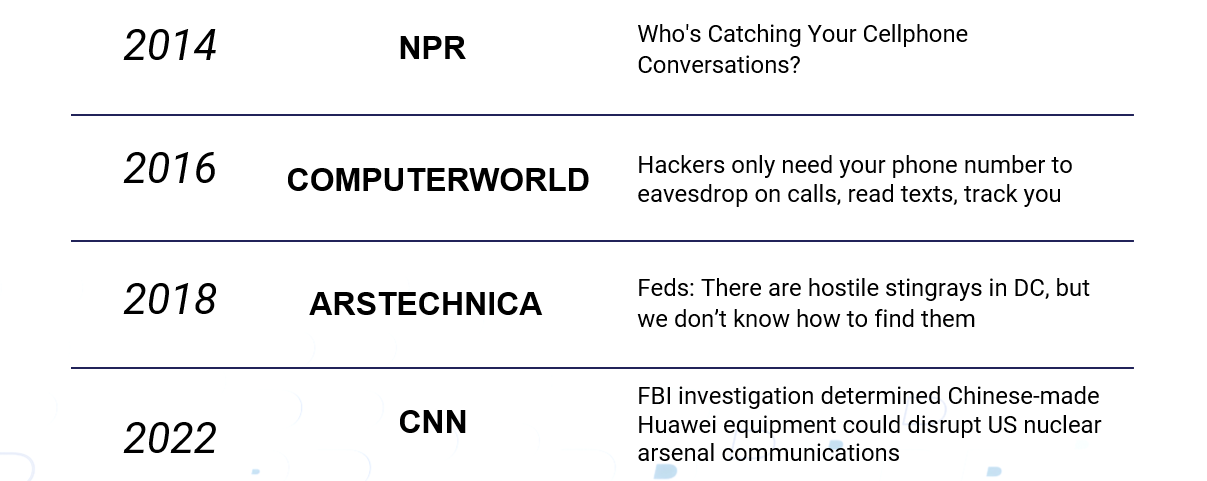
These are just a few recent examples that reveal the risk of intercepted communications. Consider these headlines over the years:
What can governments and agencies do about this risk — and what should they do? I shared some answers recently at the Advanced Technology Academic Research Center (ATARC) and Government Information Technology Executive Council (GITEC) conference, during my presentation, "The Rise of Interception and Espionage: How to Prevent it and Ensure Communications and Data Security."
Secure Communications Use Cases for Government
BlackBerry has deep roots and decades of expertise in the area of secure communications. BlackBerry® SecuSUITE® is relied upon by governments to communicate securely, regardless of where their people are, or with whom they must collaborate. While there are many relevant use cases to choose from, I’d like to examine the top three.
Many governments collaborate across agencies that aren't necessarily on the same networks. Often, they need to deal with partners in multiple countries and it’s not possible to provision everyone into your own secure network. In this use case, you must connect teams together securely via other means. One approach is to employ common data policies; this is particularly important for international collaboration because different countries have different policies around data retention. Consider the following best practices for this use case:
- There should be no need to give other organizations access to your internal systems or networks.
- There should be no need for specialized hardware.
- There should be no sharing of real phone numbers.
- There must be configurable data sharing and records collection policies.
- There must be a maintenance chain of custody for data collected for security and compliance.
- The optimal approach will allow a dynamic mission-driven user base with remote activation and deactivation that requires no end-user engagement.
Use Case #2: Securing Deployed Teams’ Personal Devices
In this use case, your people travel and communicate back to their home country or home office via local networks that could be insecure or tapped. Keep these issues in mind when allowing deployed team members to use local communication channels:
- Business and personal calls frequently share private or confidential details. (Intercepted calls between soldiers involved in the Ukraine conflict and their families are a great example of why all employee communication back home should be secure.)
- Look for an approach that is SIM-card-independent; in addition to increasing security, this also eliminates international roaming fees.
- Offer the ability to connect to the public phone network in your home country securely from overseas.
- Decrease visibility by using regular off-the-shelf phones in order to avoid drawing unwelcome attention.
Use Case #3: Reclaiming Out-of-Band, Compromised Communications
This use case is something that should be included in more disaster recovery and business continuity plans. How do you communicate securely, even when primary networks are either compromised or unavailable? The BlackBerry IR (incident response) team has seen too many examples of cyberthreat actors compromising typical collaboration tools during a data breach, as described in this recent blog excerpt:
“Communications about security incidents are often highly confidential and sensitive. The last thing you can afford to do is accidentally share your response plans with the attackers themselves. Sometimes an incident might be linked to an insider threat, or the attacker has access to internal email or online collaboration tools such as Slack.
“Also, on multiple occasions, our incident response team witnessed administrators using cleartext email to send credentials and other sensitive information during an incident. APT (advanced persistent threat) actors often have full control over email servers and have performed network surveillance to extract credentials from cleartext traffic. In one case we saw the threat actor reuse credentials created for the incident response teams’ recovery actions.”
— The Sixth Deadly Sin of Incident Response
For all these use cases, organizations should find a tailored solution that is easily implemented.
BlackBerry SecuSUITE
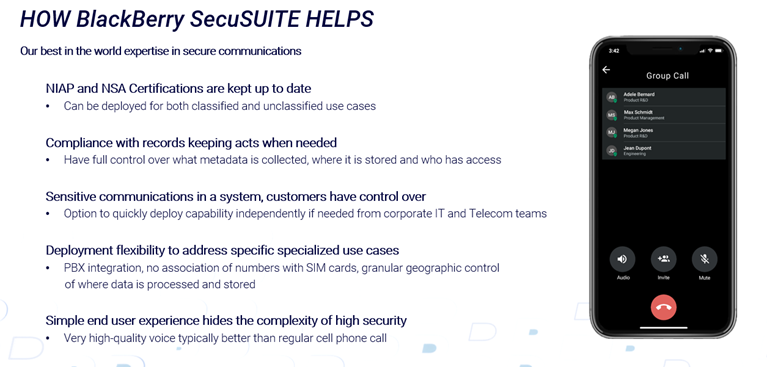
If your organization requires high-security voice and messaging for iOS® and Android™ devices, consider this: BlackBerry SecuSUITE for Government 5.0 was recently awarded updated NIAP (National Information Assurance Partnership) certifications and listed as a CSfC (Commercial Solutions for Classified)-compliant product. These certifications verify that BlackBerry SecuSUITE meets the highest security requirements for both the United States Federal Government and the broader Five Eyes intelligence alliance.
Here are the ways BlackBerry SecuSUITE can help your government, agency, or enterprise organization secure its communications.
Final Thoughts
We’re proud that BlackBerry SecuSUITE continues the BlackBerry legacy of secure communication combined with ease of implementation. NATO’s recent choice of the platform further validates our work. If we can help your organization, please reach out to me.